In my previous post i have explained on how to replace VMCA SSL certificate on on vCSA 6.7 with embedded PSC , this post I will be sharing the information on replacing self-signed certificate by a Certificate Authority (CA) signed SSL certificates in a vCenter External PSC 6.7 environment.
The vSphere Certificate Manager utility provides all workflows to replace or regenerate the Machine SSL Certificate, Solution User Certificates and the VMCA Root Signing Certificate on the vCenter Server and Platform Services Controller.

Requirements
- Working PKI based on Active directory Certificate Server.
- Certificate Server should have a valid Template for vSphere environment
Note :- If you don’t have a template Refer this Post for creating a new Template
- vCenter Server Appliance with root Access
Generate a certificate request from PSC 6.7
Login to vCSA by using SSH or Console
Run /usr/lib/vmware-vmca/bin/certificate-manager and select the operation option 1

Note:-This console is already in bash shell so it didn’t asked type shell to access console , in you case it may asked you type shell to access
Enter administrator credentials and enter option number 1.

Specify the following options:
- Output directory path :- path where will be generated the private key and the request
- Country :- your country in two letters
- Name :- The FQDN of your PSC
- Organization :- an organization name
- OrgUnit :- type the name of your unit
- State :- country name
- Locality :- your city
- IPAddess :- provide the PSC IP address
- Email :- provide your E-mail address
- Hostname :- the FQDN of your PSC
- VMCA Name :- the FQDN where is located your VMCA , here we use PSC (vCSA or PSC FQDN based on your setup)

Once the private key and the request is generated select Option 2 to exit
Next we have to export the Request and key from the location , we will user win scp for this operation .
To perform export we need additional permission on PSC , type the following command for same
Note :- To perform export we need additional permission on PSC , type the following command for same
#chsh -s /bin/bash root
Once connected to PSC from winscp tool navigate the path you have mentioned on the request and download the vmca_issued_csr.csr file

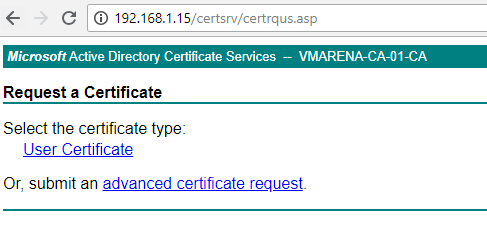
Open the Certificate Server URL using this format http://FQDN or IP /CertSrv/ from browser and select Request a certificate option

Select Advanced certificate request
Open the exported vmca_issued_csr.csr file in a notepad and copy the contents and paste ob the Column Based-64-encoded certificate Request , Select the appropriate Certificate template , here I choose vSphere 6.7 and Click on Submit

From Next Page Select the Base 64 encoded option and Download the Certificate and Certificate Chain

Note :- You have to export the Chain certificate to .cer extension , by default it will be PKCS#7
Open Chain file by right click or double click navigate the certificate -> right click -> All Tasks -> export and save it as filename.cer
Also you have to export the Certificate Server certificate .

Next you have export the newly downloaded certificates to PSC Appliance ( PSC , Chain , CA root certificates )
Login to PSC appliance using winscp and copy to location .
Note:- Remember path where you copied the new certificates , it is required for replacing menu .

Login to vCenter Server Appliance Console or using putty
Go to the path where you copied the certificates change the new PSC certificate to root-ca.cer ( Not mandatory , you can eep the same same )
Rename # mv /tmp/certnew.cer /tmp/root-ca.cer

Now you add the CA server certificate data to your new renamed PSC certificate

Now will replace the certificate
Run /usr/lib/vmware-vmca/bin/certificate-manager and select the operation option 1

Enter administrator credentials and enter option number 2
Add the exported certificate and generated key path from previous steps and Press Y to confirm the change
- Custom certificate for machine SSL :- Path to the chain of certificate (srv.cer here)
- Valid custom key for machine SSL :- Path to the .key file generated earlier.
- Signing certificate of the machine SSL certificate :- Path to the certificate of the Root CA (root-ca.cer , generated base64 encoded PSC certificate).


It will take little time to complete and you can see message
Status : 100 % Completed [All tasks completed successfully]
Note:- If you are providing different certificate instead of chain certificate in Custom certificate for machine SSL option you will get error with "depth lookup:certificate"
Also if CA server certificate data is not added to PSC root certificate and available locally on same path you may face below error

Now Connect to the vCenter using Web Client and you can see the new custom certificate

Thank you for reading this post , Share the knowledge if you feel worth sharing it.
Check more vSphere 6.7 Posts

